ALERT !!!
The Ethereum Classic network has been subjected to a 51% attack, it is recommended not to send a transaction until the situation is clarified.
Our mining pool is already validated in this respect, everything is safe and the mining process is working normally. For the above-mentioned reasons, withdrawals are suspended until the situation is clear.
The situation is worrying because the ETC is one of the largest victims of the attack, the attack has used computing power corresponding to more than 300,000 graphics cards.
The issue of 51% attacks is common in the world of cryptocurrencies – we often inform about it and we call for a more decisive public debate in this area.
Contrary to the opinion that emerges – there are solutions available that can stop this wicked practice that weakens the reputation of cryptocurrency, their adaptation and their value. It is worth pointing out several available solutions:
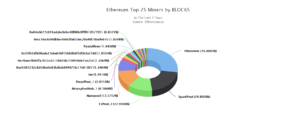
🏁The decentralization of computing power according to the POW consensus assumptions – do not share your power where it is dangerous. The sheep’s rush of miners is the Achilles’ heel of our industry. Beware of places like Nicehash, where a lot of miners makes their mining rigs avalible, which are then rented for attacks of 51%. Similarly, avoid large multipools, large mining pools – this power can be used for potential attacks. Choose mining pools that are smaller and help build the right network structure. This is a guarantee that anyone with bad intentions – be it a group of hackers, a corrupted mining pool will not be able to gain significant computing power outside of its own resources, and this makes 51% attack much harder. After all, it is difficult to gather one entity more power than the rest of the world.
🏁To condemn bad practices that accompany the extraction of cryptocurrencies, e.g. the Empty blocks phenomenon – empty blocks that some mining pools include in the network are very harmful – firstly do not contain transactions, and using such empty blocks facilitate 51% attacks – we wrote about it earlier . (without going into details).
🏁The third task – to develop solutions that make attacks difficult and above all APPLY already available solutions. PIRL GUARD is a great example that makes network attacking very difficult. Preliminary findings indicate that perhaps if Ethereum Classic added to its protocol PIRL GUARD, then the whole attack would fail.
In addition, for smaller coins, use proprietary algorithms that, due to their niche, will not be available on large centralized mining pools or computing power rentals. Thanks to this, the attackers will not get the attack tools. (See previous point).
We can continue to look at the next attacks that will take place with great certainty (who will be next?) Or start to set up particular interests and start taking responsibility for the integrity of the network. And this is a task primarily for miners. Eat humble pie those who did park their rigs on Nicehash, eat double humble pie, the ones who made their rigs available in the last 24 hours – your mining rigs were very likely used to carry out an attack on Ethereum Classic. 😖😖😖
Our mining pool supports all good practices and DEFINITELY does not use these bad practices (empty blocks and does not provide computing power to anyone indiscriminately).